Consumer spyware applications that the secret and continuous monitoring of your personal messages, photos, phone calls and real-time location is a growing problem for Android users.
This guide can help you identify and remove common tracking apps from your Android phone, including TheTruthSpy, KidsGuard and other apps.
READ OUR EXCLUSIVE RESEARCH
Consumer-grade spyware applications are often sold under the guise of child monitoring or family monitoring software, but are referred to as “stalkerware” and “spouseware” for their ability to track and also monitor partners or spouses without their consent. These spyware apps are downloaded from outside the Google Play app store, placed on a phone without a person’s permission, and often disappear from the home screen to avoid detection.
Stalkerware apps rely on abusing built-in Android features commonly used by companies to remotely manage their employees’ work phones or use Android’s accessibility feature to spy on someone’s device.
You may notice your phone acting unusual, running hotter or slower than usual, or using large amounts of network data, even when you’re not actively using it.
Checking to see if your Android device has been hacked can be done quickly and easily.
Before you start
It is important to have a safety plan in place and reliable support if you need it. Keep in mind that removing spyware from your phone will likely alert the person who planted it, which could create a dangerous situation. The Coalition Against Stalkerware offers advice and guidance for victims and survivors of stalkerware.
Please note that this guide only helps you detect and remove spyware, it does not delete the data already collected and uploaded to its servers. Also, some versions of Android may have slightly different menu options. As is typical with any advice, you follow these steps at your own risk.
Check your Google Play Protect settings
Make sure Google Play Protect, a security feature on Android phones, is turned on. Image Credits: TechCrunch
Google Play Protect is one of the best safeguards against malicious Android apps, checking apps downloaded from the Google app store and from external sources for signs of potentially malicious activity. These protections stop working when Play Protect is turned off. It’s important to make sure Play Protect is turned on to make sure it’s working and scanning for malicious apps.
You can check that Play Protect is enabled through the settings of the Play Store app. You can also scan for harmful apps if it hasn’t already been scanned.
Check if accessibility services have been compromised
Stalkerware relies on deep access to your device to access data and is known to abuse Android’s accessibility feature, which by design requires broader access to your operating system and data for screen readers to work and other accessibility features.
Android users who don’t use apps or accessibility features shouldn’t see any apps in their Android settings.
If you don’t recognize a service you’ve received in the Accessibility options, you may want to turn it off in the settings and remove the app. Some stalkerware applications disguise themselves as ordinary-looking applications and are often called “Accessibility”, “Device Health”, “System Service” or other innocuous-sounding names.
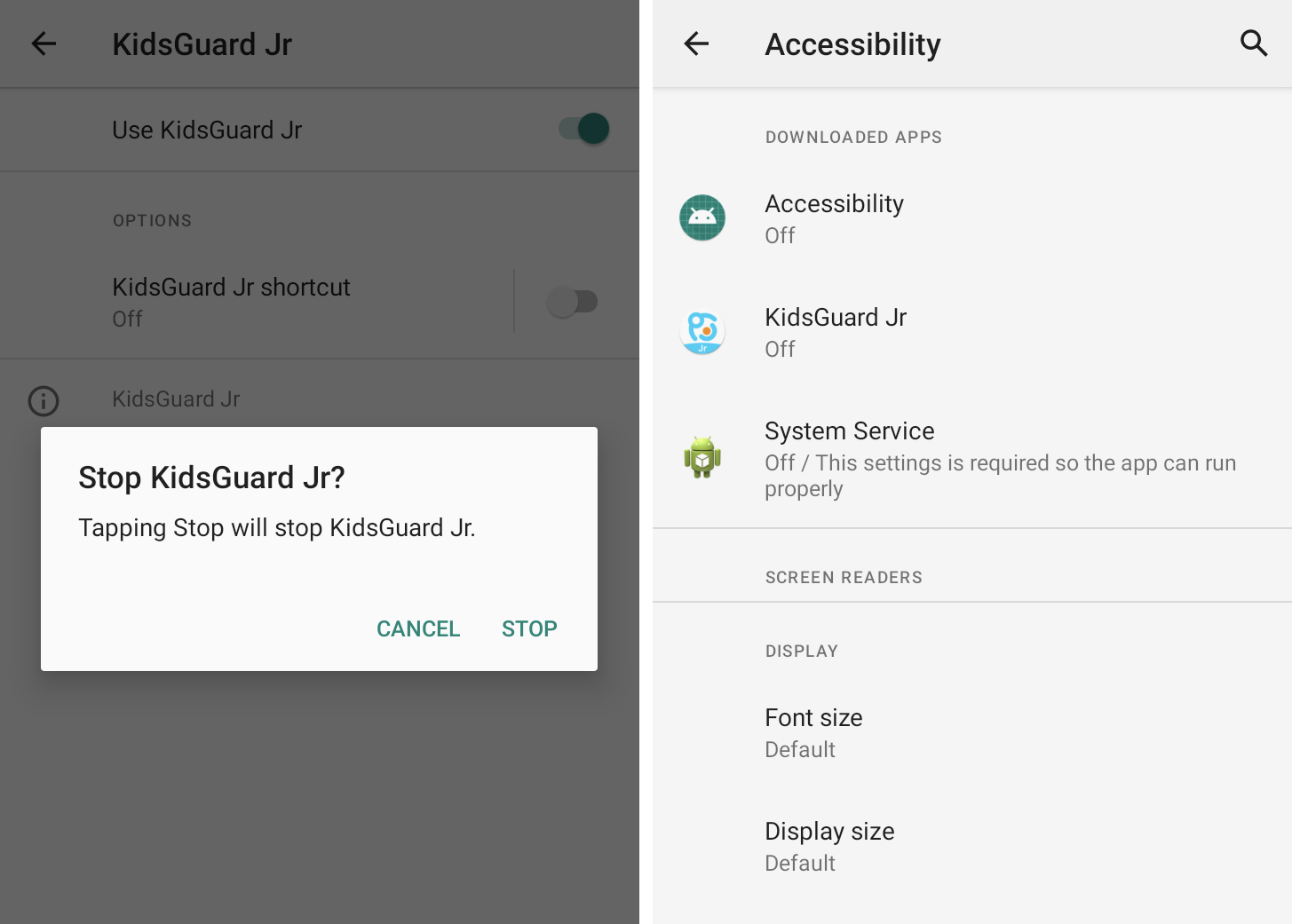
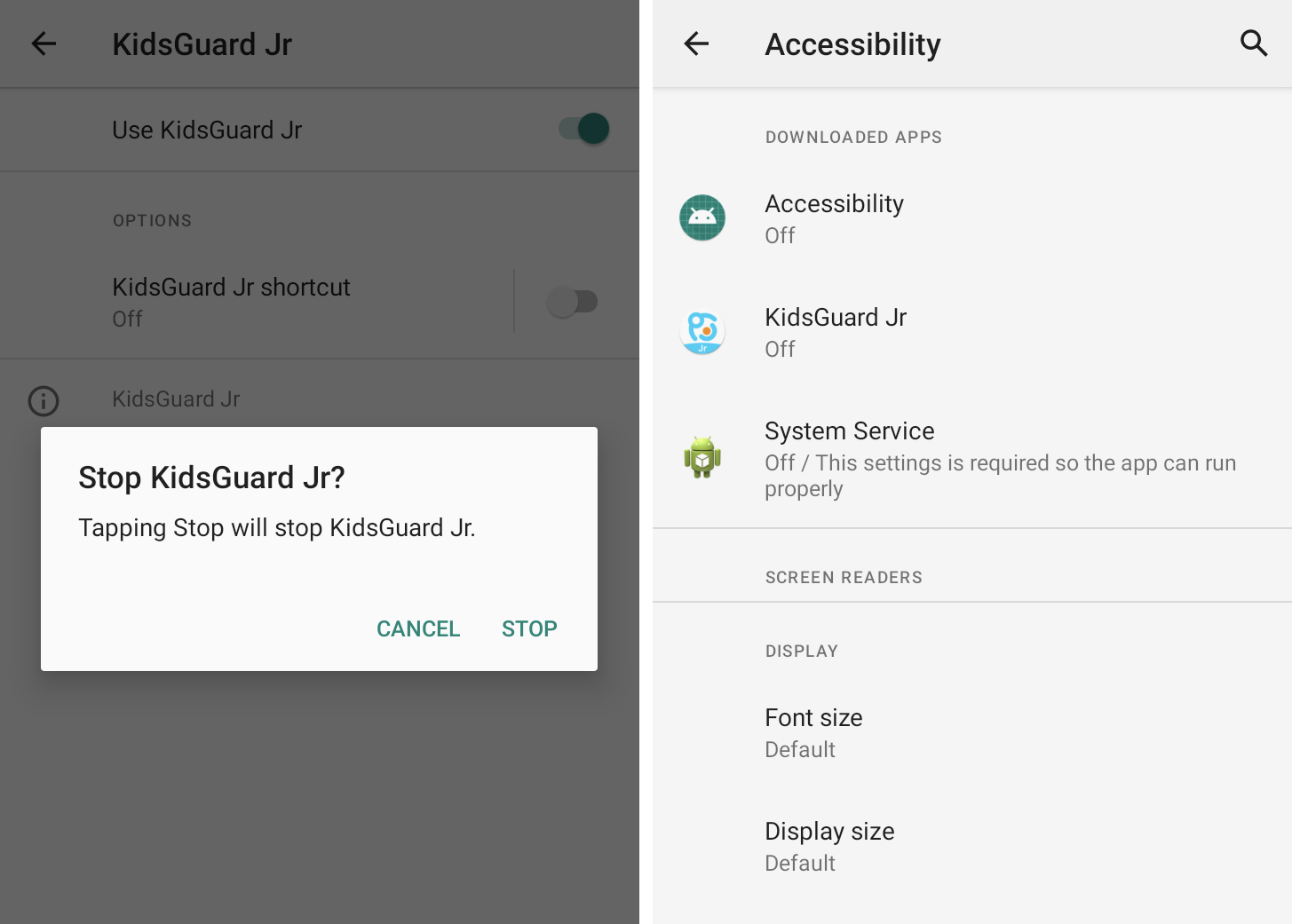
Android spyware often abuses built-in accessibility features. Image Credits: TechCrunch
Control your access to notifications
As well as accessibility features, Android also allows third-party apps to access and read your incoming notifications, such as allowing smart speakers to read notifications aloud or your car to display notifications on its dashboard. Granting notification access to a stalkerware app allows persistent monitoring of your notifications, which includes messages and other notifications.
You can control which apps have access to your notifications by checking your Android notification access settings under Special app access. Some of these apps you may recognize, such as Android Auto. You can disable notification access for any app you don’t recognize.
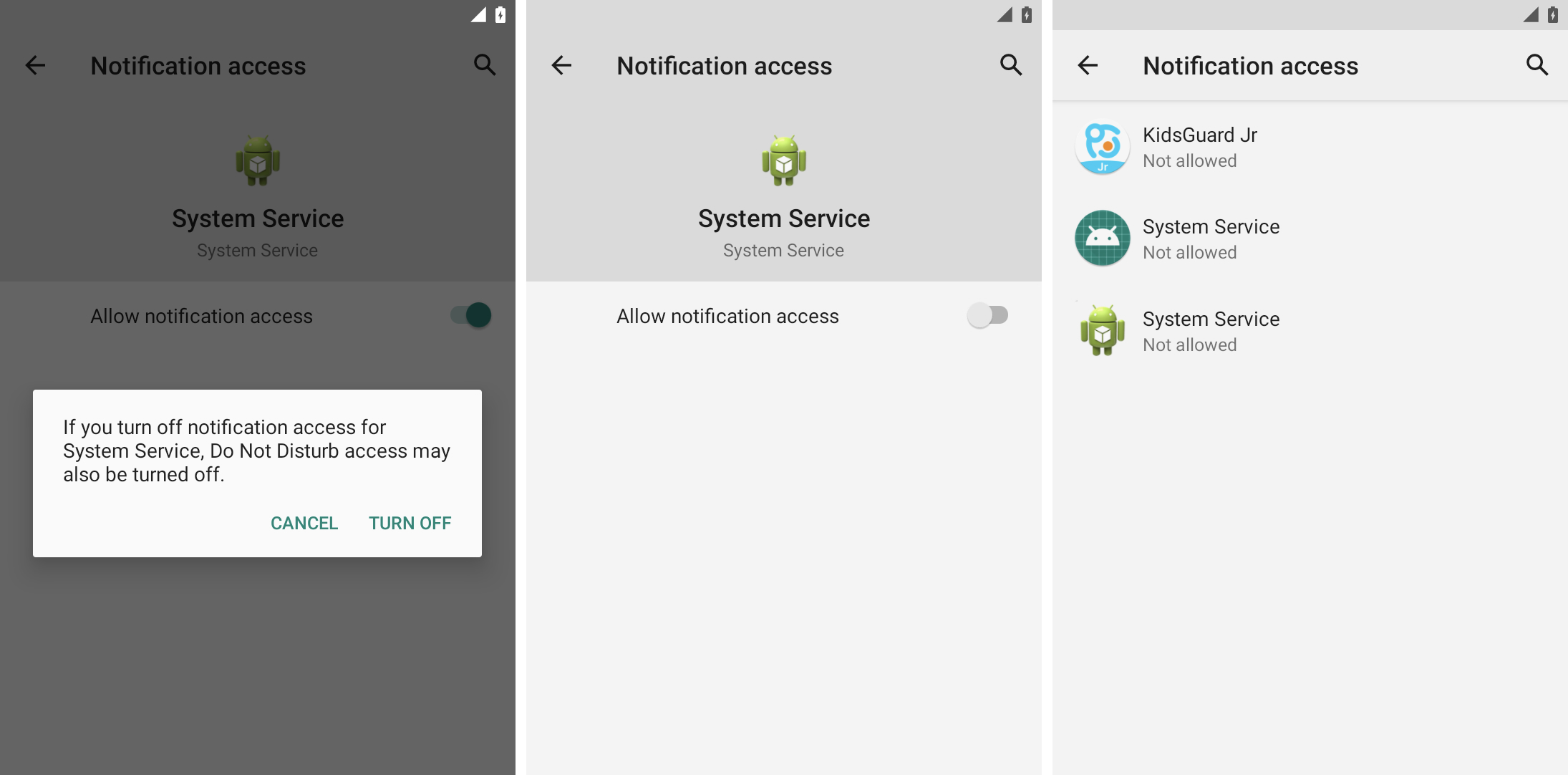
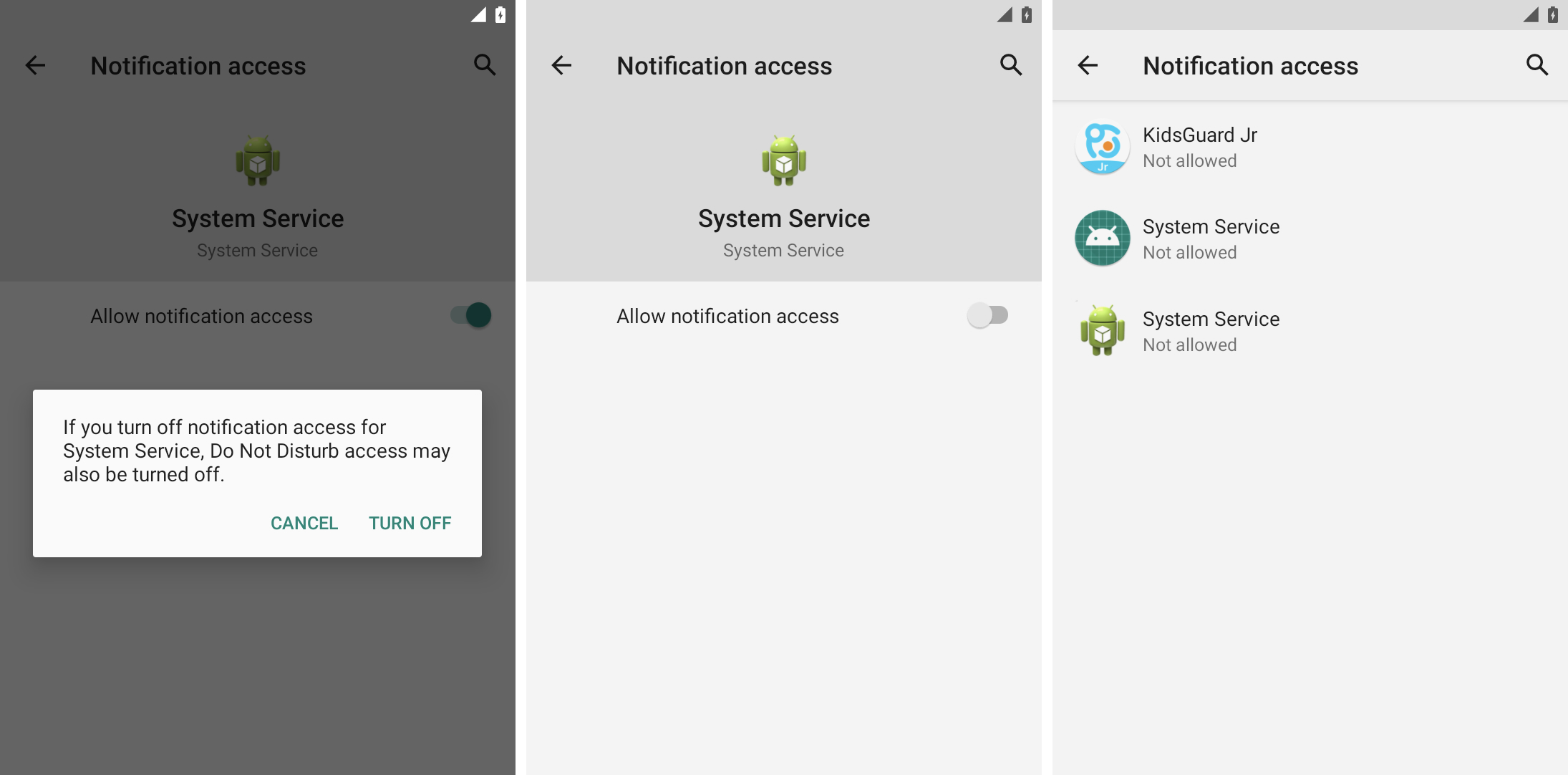
Spyware uses notification access to read user messages and other notifications. Image Credits: TechCrunch
Check if a device manager app is installed
Other features commonly abused by stalkerware are the Android device management options, which have similar but even broader access to Android devices and user data.
Device management options are commonly used by companies to remotely manage their employees’ phones, such as wiping the phone in case of device theft to prevent data loss. But these features also allow stalkerware apps to monitor your Android screen and device data.
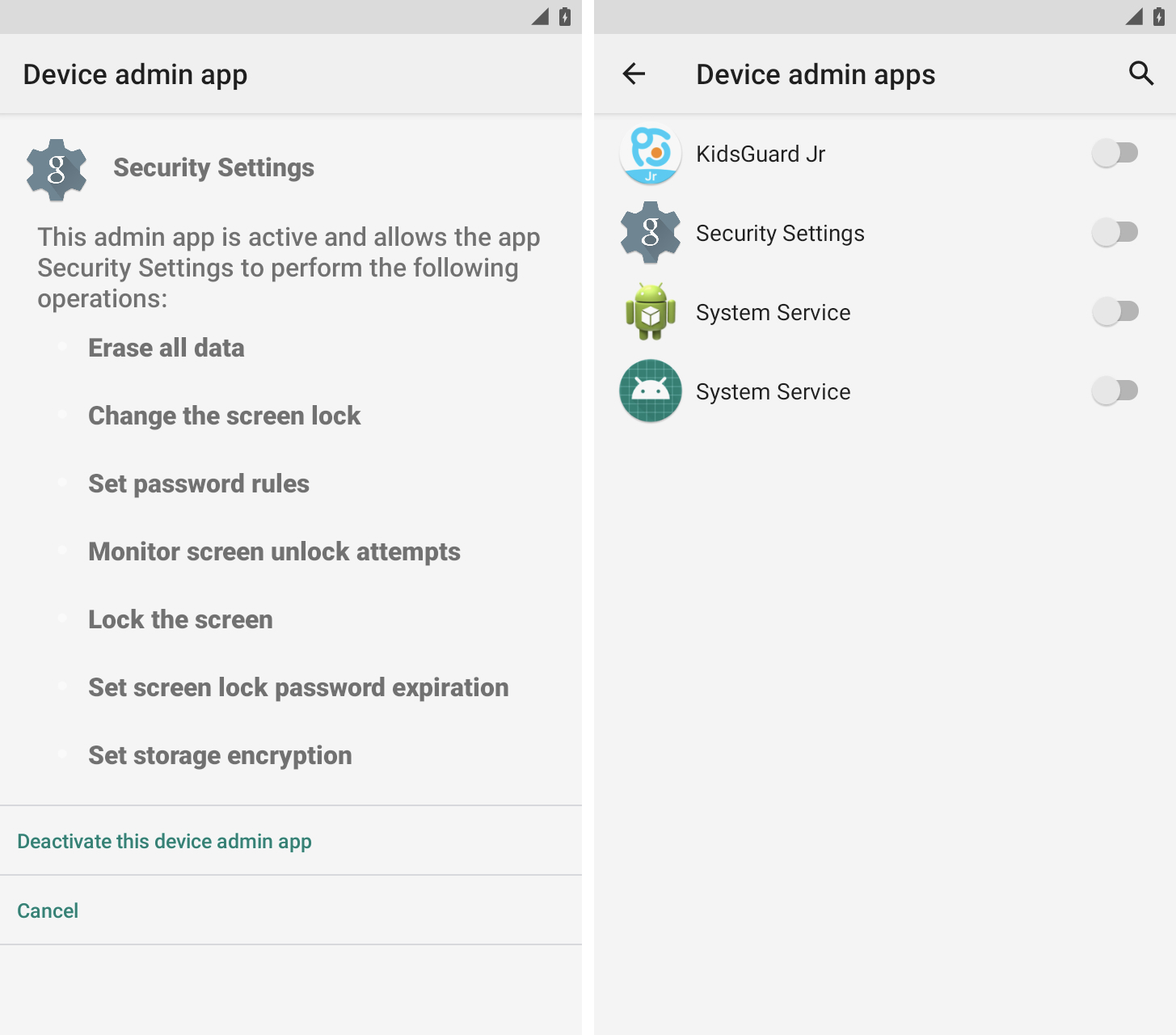
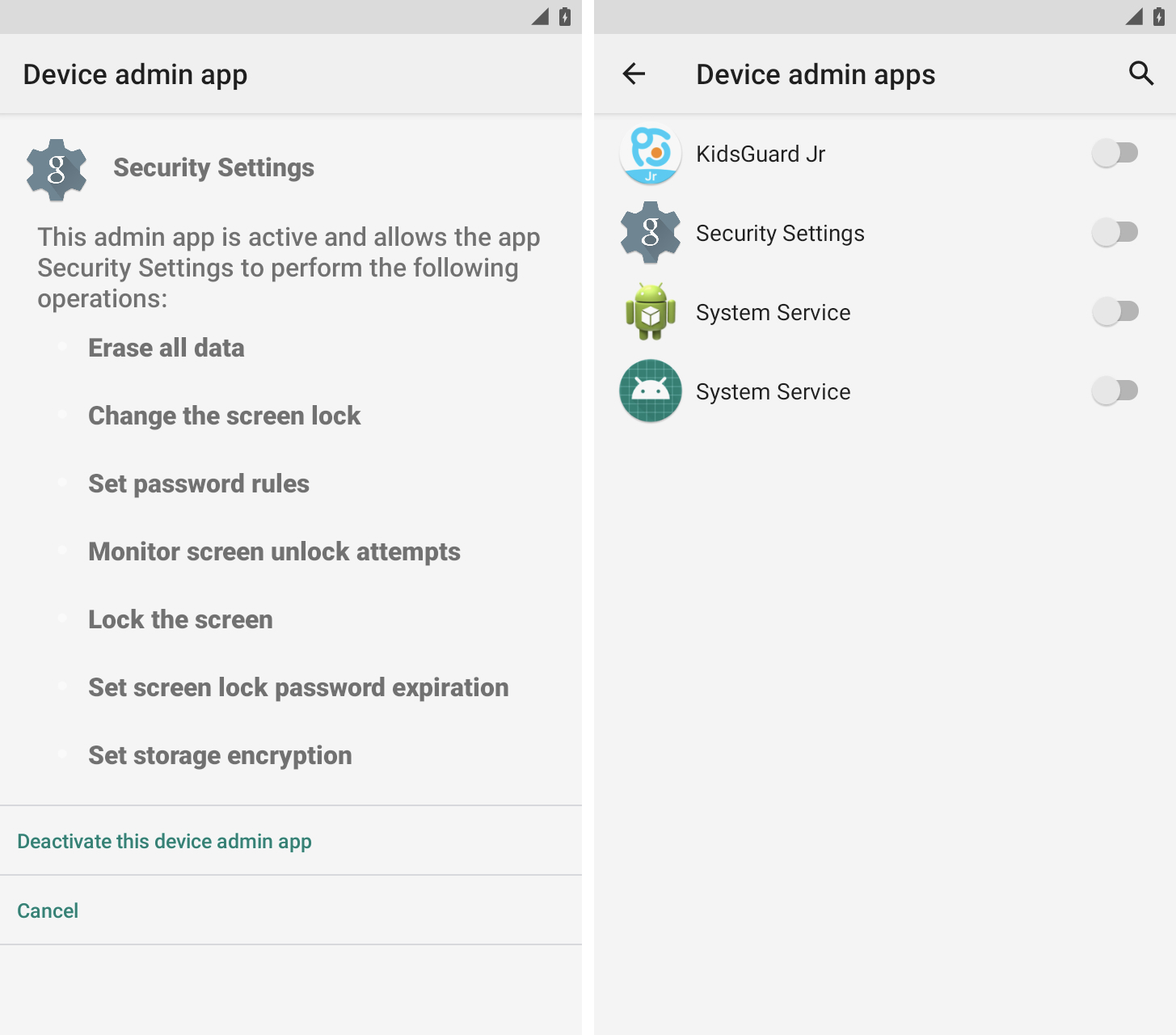
An unrecognized item in your device manager app settings is a common indicator of phone tampering. Image Credits: TechCrunch
You can find the device manager app settings in Settings under Security.
Most people won’t have a device manager app on their personal phone, so be aware if you see an app you don’t recognize with something vague and vague like System Service, Device Health, or Device Manager. ” .”
Check apps to uninstall
You may not see a home screen icon for any of these stalkerware apps, but they will still appear in your Android device’s app list.
You can see all installed apps in Android settings. Look for apps and icons you don’t recognize. These apps may also appear to have broad access to your calendar, call logs, camera, contacts, and location data.
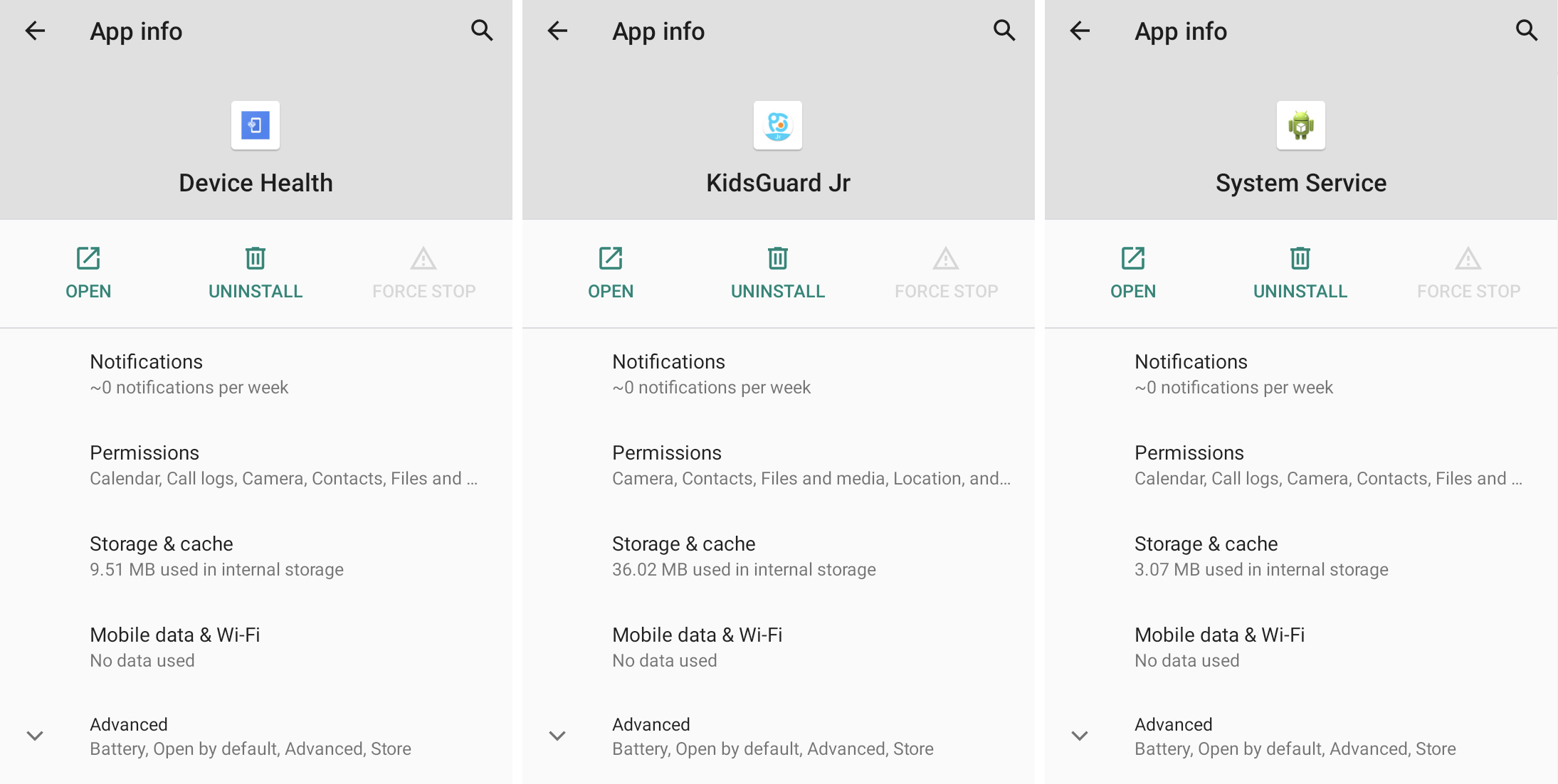
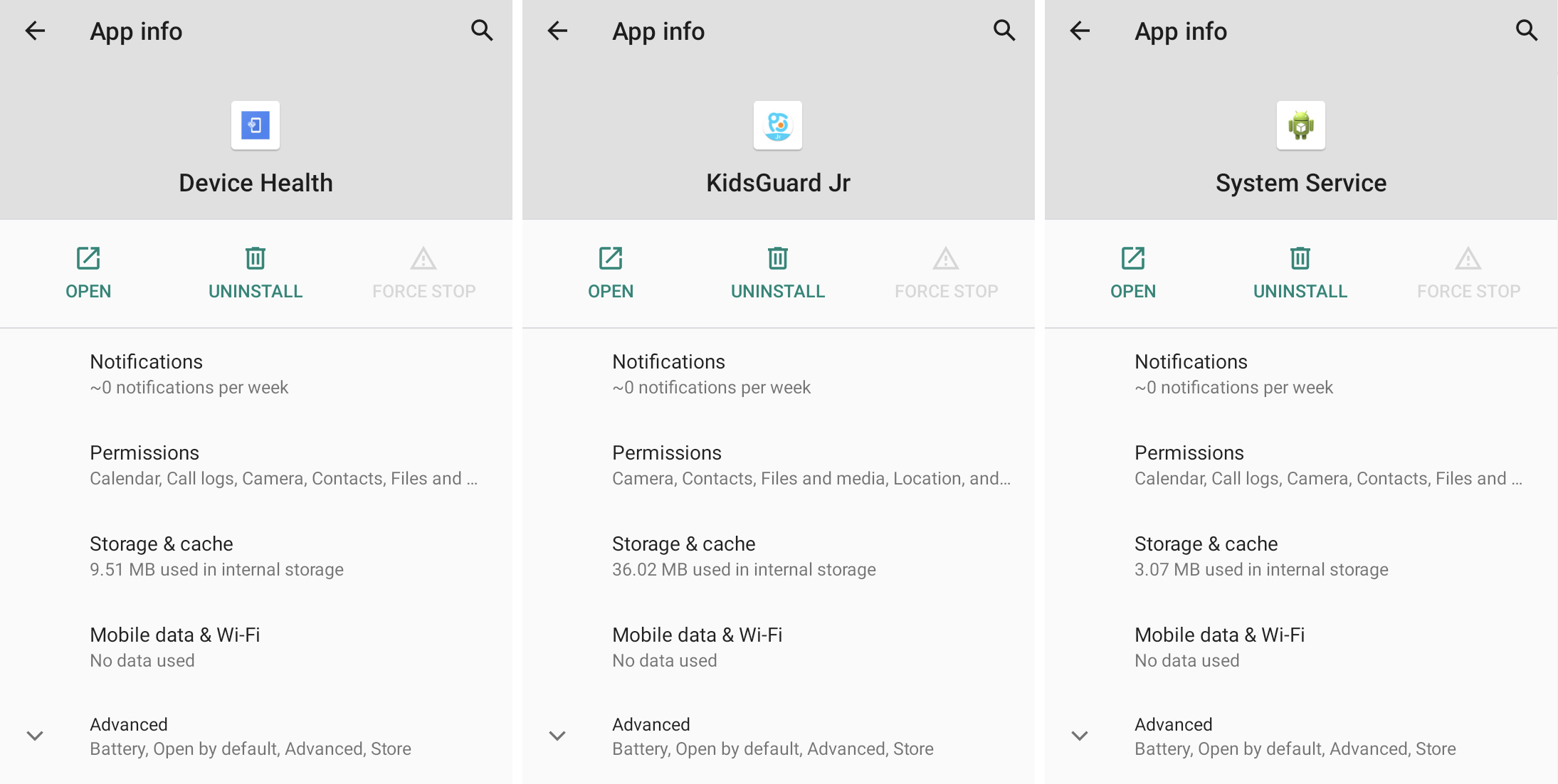
Spyware applications are designed to match names and icons that have a generic appearance. Image Credits: TechCrunch
Force stopping and uninstalling a stalkerware application will likely notify the person who installed the stalkerware that the application no longer works.
Secure your device
If stalkerware was planted on your phone, there’s a good chance your phone was unlocked, unprotected, or your screen lock was guessed or learned. A stronger screen lock password can help protect your phone from intruders. You should also protect email and other online accounts by using two-factor authentication where possible.
If you or someone you know needs help, the National Family Violence Hotline (1-800-799-7233) provides free, confidential 24/7 support to victims of domestic abuse and violence. If you are in an emergency, call 911. The Coalition Against Stalkerware has resources if you think your phone has been compromised by spyware.
Read more at TechCrunch:
